
The Black Dog, a restaurant and pub in London, England, is suddenly crowded.
Read More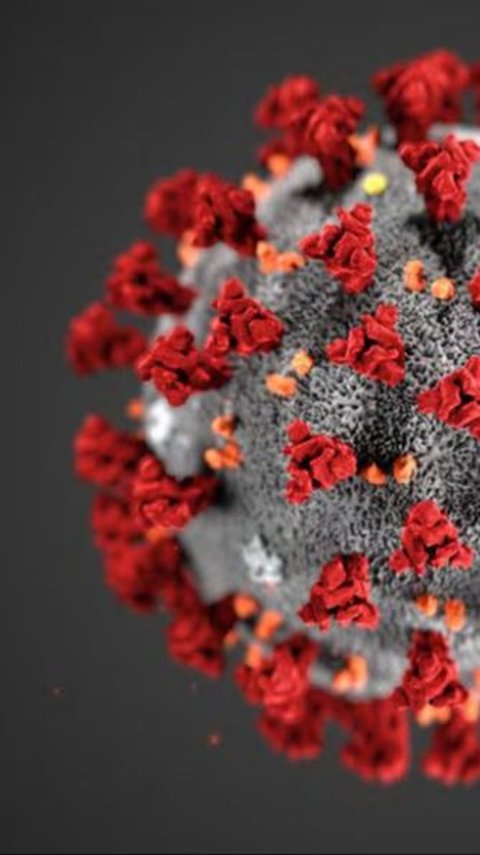
Dutch researchers recently reported the longest known case of SARS-CoV-2 infection.
Read More
Here are some of the hottest girl ever appeared in Fast & Furious series.
Read More
Scorpios cherish their alone time for reflection and recharge. Plus, they make connections with those who trulys understand them.
Read More
Here are some of the best time travel movies you should add to your watch list.
Read More
Kristen Stewart movies have something action-packed for everyone.
Read More
Survival horror games are a popular genre that combines elements of horror fiction with challenging gameplay.
Read More
Let these Jurassic Park quotes inspire you to revisit the thrilling world of dinosaurs.
Read More
This surprising plan gets mixed reactions by many people.
Read More
If you are looking for some amazing offbeat destinations in Italy, here are the top 8 hidden gems in Pizza country to add to your bucket list.
Read More
The 1990s was the decade when Hollywood gave rise to many actresses who became cultural icons.
Read More
Kent is a treasure trove of historical sites that will delight visitors of all ages. There is something for everyone to enjoy in this beautiful county.
Read More
Are you a chocolate and sweet lover? If so, this chocolate pie recipe will surely delight your taste buds.
Read More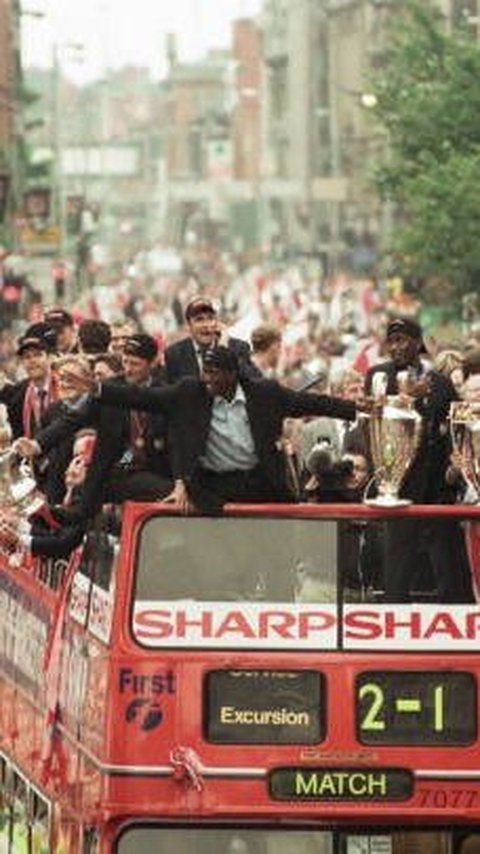
The documentary will also shows several legendary players during the club's big success.
Read More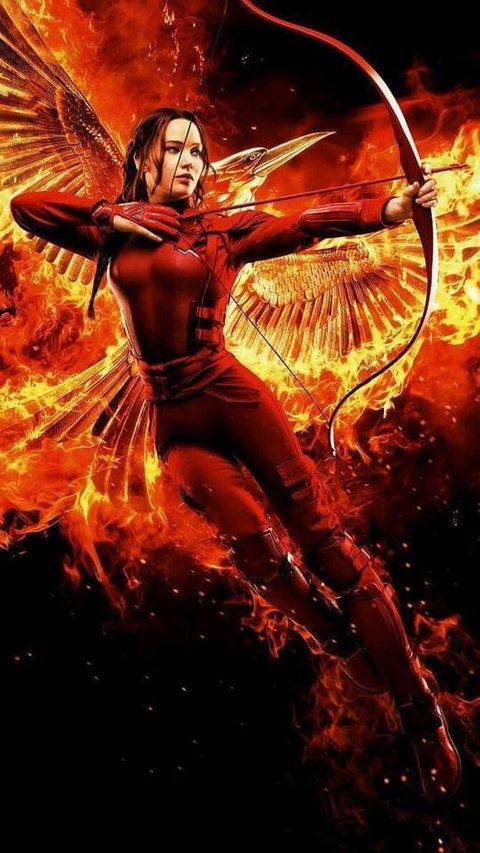
Moved by these movies, people started memorizing their iconic lines and calling them Hunger Games Quotes.
Read More
Learning what helps with period cramp will help you to ease the pain during your period.
Read More
Camden has it all, whether you're looking for a relaxing stroll along the canal or a lively night at a music venue.
Read More
Gardening is an enjoyable hobby that needs a lot of passion and patience. These gardening quotes will help you to fall in love even more with this hobby.
Read More
The content creator is successfully turns the carbonated drink into wine!
Read More
Dealing with a narcissistic person can be exhausting, but these great narcissism quotes can help you to deal with them.
Read More
Why does Milan city government wants to ban one of the most iconic foods in Italy?
Read More
Combining these Kim Kardashian beauty tips into your skincare routine can help you get flawless and radiant skin.
Read More
Like the metamorphosis, these quotes about butterflies reflect on personal growth, change, and the beauty of life's transformations.
Read More
A Japanese Twitter user named Tomo recently completed one of the most challenging puzzles.
Read More
Lloyd Martin has wanted to run a marathon for years.
Read More