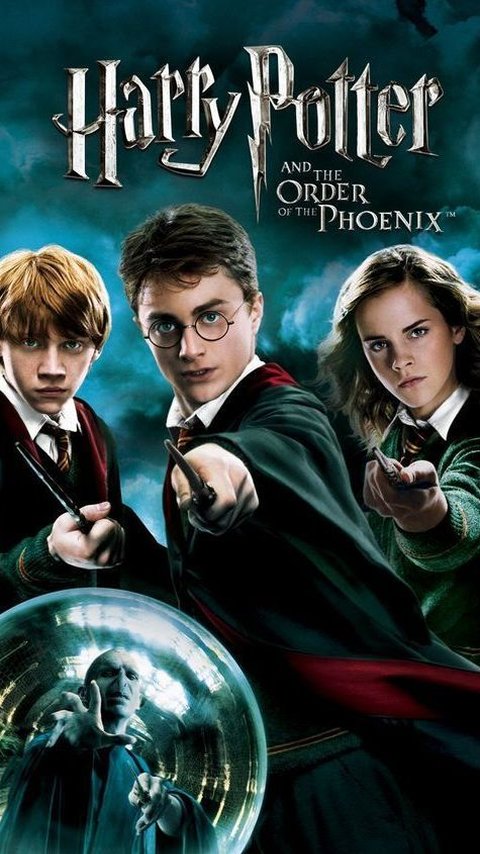
50 Harry Potter Jokes: Hilarious Jokes That Will Tickle Your Funny Bones
If you are a fan of Harry Potter, you should check out these hilarious Harry Potter quotes that will make you rolling on the floor laughing.
Read More
Deadpool and Wolverine Unite to Fight Cassandra Nova in the Latest Trailer
Marvel Studios officially released the latest Deadpool & Wolverine trailer on Monday (4/22) US time.
Read More
35 Family Love Quotes that Capture the Essence of Home
Let's dive into a collection of family love quotes that capture the heartwarming feeling of home.
Read More
Nigerian Man Breaks 58-Hour Chess Record to Raise Money for Education
A Nigerian chess champion has broken the world record after playing for 58 hours without stopping.
Read More
James Hetfield Gets New Tattoo Using Lemmy Kilmister's Cremation Ashes
Metallica frontman James Hetfield shows off a new tattoo on the middle finger of his right hand.
Read More
7 Most Beautiful Female Basketball Players
Here are the top 7 most beautiful female basketball players in the world.
Read More
5 Horror Movies Similar to 'Immaculate'
"Immaculate" is a horror film that follows Sister Cecilia, who is is inexplicably pregnant and said was in immaculate conception
Read More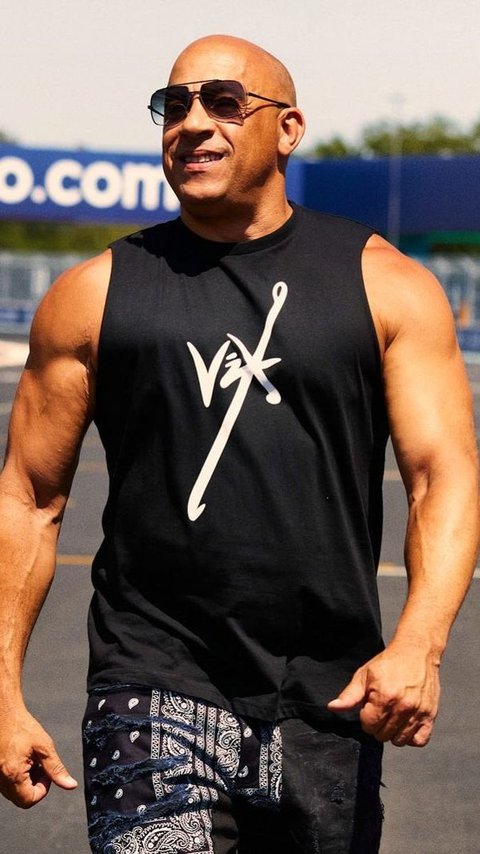
Top 5 Vin Diesel Movies Outside Fast & Furious
Here are the top 5 best Vin Diesel movies outside Fast & Furious you must watch.
Read More
Meet Amanda Nguyen, the First Southeast Asian Woman to Fly in Space
She will be the first Vietnamese Woman to fly to space, according to Space for Humanity.
Read More
25 Life Is Beautiful Quotes to Help You Enjoy Every Moment of Your Life
These life is beautiful quotes will remind you to cherish the moment and find joy in the little things.
Read More
5 Unique Facts About Earth Day You Probably Don't Know
Earth Day is an annual event celebrated around the world on April 22 to demonstrate support for environmental protection.
Read More
7 Best Places to Visit in Argentina
From the lively capital city of Buenos Aires to the charming Ushuaia on the southernmost tip of the world, here are the best places to visit in Argentina.
Read More
42 Tuesday Motivation Quotes for A Productive Week
Tuesday motivation quotes are words of inspiration to help us start our week with energy and enthusiasm.
Read More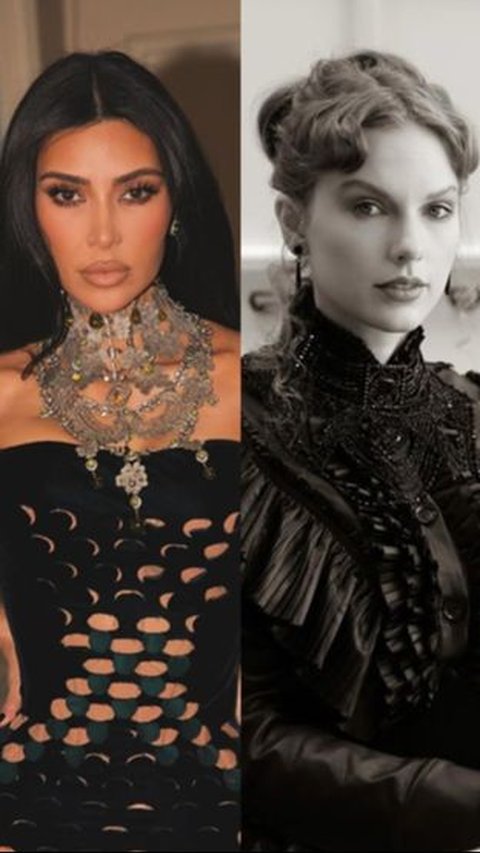
Kim Kardashian Lost Over 100,000 Followers After Taylor Swift 'Included' Her on New Album
Kim Kardashian has been losing about 120,000 followers so far.
Read More
35 Inner Peace Quotes for Peaceful Living and Calm Mind
These inner peace quotes will help you to reach a peaceful life.
Read More
Simple Shortbread Cookie Recipe With Only 4 Ingredients
If you want to make something simple to satisfy your sweet tooth, you should try our shortbread cookie recipe.
Read More
Cave in Kenya Believed to be Source of Ebola
The cave turned out to be home to some of the deadliest viruses in human history.
Read More
How to Wash a Weighted Blanket Properly in 2 Ways
Learning how to wash a weighted blanker properly can help to maintain its cleanliness and hygiene as well as make sure it can last long.
Read More
Pet Loss Quotes: 30 Healing Words for Grieving Hearts
These quotes can also support us during this emotional journey.
Read More
Tom Holland Gives Another 'Update' For The Upcoming Spiderman 4
The 27-year-old actor gives a new statement about the rumored movie.
Read More
30 Determination Quotes to Encourage You to Achieve Your Goals
These determination quotes will spark your spirit to make your dream comes true.
Read More
Fortnite Allows Players to Hide "Confrontational Emotes" in A New Update
"Certain emotes that are sometimes used in confrontational ways."
Read More
45 Quotes About Lies to Help You Deal with Dishonesty
These quotes about lies might help you express your mixed feelings.
Read More
Inter Milan Officially Win Serie A And Get "Two Stars"
Nerazzuri secure their Serie A title in the Derby della Madonnina.
Read More
Sony Patents 'Auto Play' Feature for Its Video Games. What Is That?
If you want to relax and watch your video game progress continue by its own, this feature may be perfect for you.
Read More